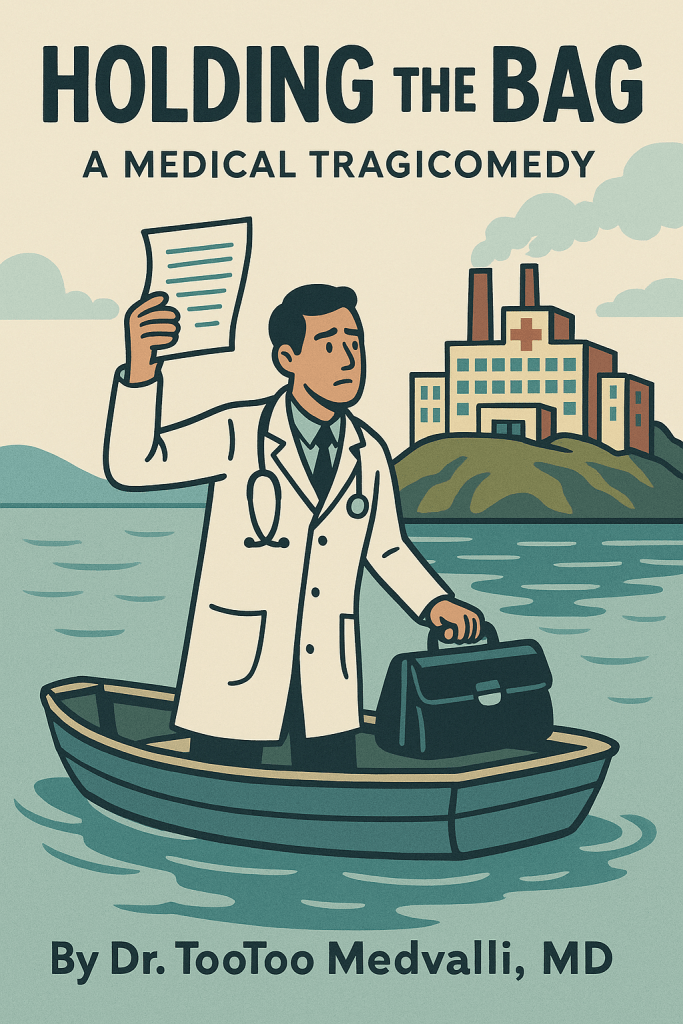
By Oskar Rausch
Being a True and Accurate Account of the Founding of the World’s Smallest Landlocked Nation, as Told by the Ministry of Information and Shawarm
Second Printing, with Additional Materials from the Archives of the People’s Tribunal

PART ONE: GENESIS
The revolution began, as most revolutions do, over garbage.
Not metaphorical garbage—the spiritual refuse of tyranny or the moral detritus of oppression—but actual garbage. Specifically, the thirty-seven Hefty bags that had accumulated behind the Al-Kareem Family Restaurant over a period of six weeks while Ypsilanti Charter Township debated whether waste management fell under “essential services” or “quality of life amenities.”
“Essential,” argued Supervisor Peb Stumbles, “implies necessity. People want their garbage picked up. But do they need it?”
The motion to table the discussion passed 4-3.
This was, it should be noted, the seventeenth consecutive year that Peb Stumbles had served as Township Supervisor. This was also the seventeenth consecutive year that Peb Stumbles had been the only name on the ballot for Township Supervisor. These two facts were not unrelated.
The ballot, in Ypsilanti Township, was less an instrument of democracy and more a formality—a rubber stamp applied to decisions that had already been made by virtue of no one else wanting the job, or perhaps by virtue of no one else knowing the job existed, or perhaps by virtue of a political machine so perfectly optimized that it had eliminated the inefficiency of opposition entirely.
“Are you running for Supervisor?” residents would be asked, every four years, by a canvasser who already knew the answer.
“Is anyone else running?” residents would reply.
“Peb Stumbles is running.”
“Then no.”
And so Peb Stumbles would win, again, with the kind of margins that would make autocrats blush—not through fraud or intimidation, but through the simple expedient of being the only option. She had never faced an opponent. She had never needed to campaign. She had never, in seventeen years, been required to explain to voters why she deserved their support, because “deserved” implied a choice, and choice implied alternatives, and alternatives did not exist.
Her platform, such as it was, consisted of continuing to do whatever she had been doing, which was difficult to evaluate because no one was entirely sure what that was.
“What does the Township Supervisor actually do?” Farid Mansour had asked once, at a community meeting.
“Administrative oversight,” Peb Stumbles had replied.
“Of what?”
“Township functions.”
“Which functions?”
“The ones that require oversight.”
The conversation had not progressed further. Farid had left with the distinct impression that he had learned nothing, which was, in its own way, informative.
To be fair, Ypsilanti Charter Township did technically have waste collection. Waste Management—the company, not the concept—arrived weekly to collect trash with the reliability of a metronome. The trash service was, in fact, adequate.
The recycling was another matter.
Recycling collection occurred every other week, on a schedule that seemed to have been designed by someone who had never seen an Amazon box. In the intervening fourteen days, a typical household would accumulate:
- 4-7 Amazon boxes (Prime membership being the only reliable service in the township)
- 2-3 Chewy boxes (for residents whose pets ate better than they did)
- 1 HelloFresh box (abandoned after the second week, but the boxes kept coming)
- Miscellaneous cardboard from Target, Walmart, and the inexplicable number of things that now arrived in boxes instead of being purchased at stores that no longer existed
By day ten, the recycling bin was full. By day twelve, residents faced a choice: store cardboard in their garages like hoarders preparing for an apocalypse, or simply throw it in the trash.
Most chose the trash.
“It’s still going to a landfill anyway,” residents told themselves, which was probably true but felt like a moral failing nonetheless.
The result was that Waste Management’s weekly trash collection had become, in effect, trash-and-recycling collection, while the biweekly recycling pickup serviced bins that were either overflowing (for the optimists) or empty (for the realists who had given up). The recycling truck would roll through the neighborhood, lift bins that contained a single flattened cereal box and three wine bottles, and move on—a ghost service, a vestigial limb of environmental aspiration.
The thirty-seven Hefty bags behind Al-Kareem’s included at least fifteen bags that were exclusively cardboard—Amazon boxes, mostly, broken down and stuffed into bags because the recycling bin had been full since the Carter administration.
“We could take it to the recycling center ourselves,” Omar had suggested once.
“The recycling center is in Ann Arbor.”
“So?”
“It closes at 4 PM. On weekdays. And it’s not open on the weekends when people actually have time.”
The cardboard went in the trash. The trash accumulated. The revolution approached.
Meanwhile, on the same evening as the garbage debate, Farid Mansour received his eleventh citation for “unmaintained vegetation exceeding 7.5 inches” from a man in cargo shorts who had materialized from behind a Honda Odyssey with a tape measure and the dead eyes of a community college adjunct who had made precisely one consequential decision in his life and intended to enforce it absolutely.
“But my neighbor—” Farid gestured toward a property that could charitably be described as “where lawnmowers go to die” and less charitably as “evidence.”
“Not my assigned block,” said the man, who was technically named Gerald but whom history would remember only as “Cargo Shorts.” He wrote the ticket with a mechanical pencil. The graphite was 0.5mm. He’d specified this at Staples.
Gerald was a “volunteer ordinance officer,” which meant he had no salary, no training, and no accountability—only a clipboard, a measuring tape, and the burning conviction that grass height was a moral issue. He had applied for the position after retiring from a middle-management role at a company that no longer existed, and he had been given the clipboard without interview, background check, or psychological evaluation.
“We need more community involvement,” Peb Stumbles had said, when the volunteer ordinance program was announced. “This empowers residents to take ownership of their neighborhoods.”
What it actually empowered was Gerald, specifically, to take ownership of everyone else’s lawns.
The program had no oversight. There was no appeals process. There was no way to contest a citation except by attending a Township board meeting, which occurred on the third Tuesday of every month at 4:30 PM—a time carefully chosen to ensure that anyone with a job could not attend.
“Why 4:30?” a resident had once asked.
“It’s when the board is available,” Peb Stumbles had replied.
“But residents aren’t available at 4:30. We’re at work.”
“Then they should prioritize.”
The resident had not prioritized. No one prioritized. The meetings were attended by Peb Stumbles, the four board members who had also run unopposed, and occasionally Gerald, who came to report on his enforcement activities with the enthusiasm of a man who had finally found his calling.
To understand Zebsilanti, one must first understand the law enforcement apparatus of Ypsilanti Township—a phrase that here means “the absence of law enforcement covered by a gossamer tissue of paperwork.”
The Township had no police department. This was a point of civic pride, in the same way that a man who has sold his car might speak proudly of his “reduced carbon footprint.” Instead, residents paid taxes to Washtenaw County, which in turn dispatched Sheriff’s deputies to respond to calls.
“We’ve chosen a regional approach to public safety,” Peb Stumbles had explained, in one of her rare public statements. “It’s more efficient.”
“Efficient for whom?” a resident had asked.
“For the region.”
The system worked as follows:
- A resident would witness or experience a crime.
- The resident would call 911.
- A dispatcher would take the information and assign a priority level, ranging from “Urgent” to “Eventual” to “Theoretical.”
- Between forty-five minutes and four hours later, a deputy would arrive.
- The deputy would take notes.
- The deputy would leave.
- Nothing would happen.
The notes themselves were a marvel of bureaucratic impressionism. Deputy Marcus VanDamn—Badge #4471, known locally as “The Stenographer of Sorrows”—had developed a particular style that residents had come to recognize. His reports read like haiku composed by a man who had stopped listening after the first sentence:
Complainant states: neighbor “threatened” him.
Neighbor states: did not.
No witnesses. No injuries.
Civil matter. Unfounded.
It did not matter that the “threat” had been delivered via bullhorn at 3 AM. It did not matter that seventeen neighbors had signed a petition. It did not matter that someone had uploaded burned a CD with a video entitled “YPSI TOWNSHIP PART 47.” Deputy VanDamn had a form. The form had boxes. The boxes did not include “watched the video.”
“But there’s footage,” residents would say.
“I can note that footage exists,” Deputy VanDamn would reply, writing footage allegedly exists in Box 14-C, which was labeled “Additional Comments (Optional).”
The footage was never watched. Box 14-C was never read. The reports were filed in a building in Ann Arbor where they achieved a kind of quantum immortality—simultaneously existing and not existing, referenced in theory but never consulted in practice.
Residents had attempted to raise this issue with Township leadership. They had written letters. They had attended the 4:30 PM meetings (those who could). They had spoken during the public comment period, which was limited to three minutes per speaker and which Peb Stumbles monitored with a stopwatch.
“Your three minutes are up,” she would say, at exactly three minutes, regardless of whether the speaker was mid-sentence.
“But I haven’t finished—”
“You’ve finished your three minutes.”
The letters were acknowledged with form responses. The public comments were noted in the minutes, which no one read. And the Sheriff’s deputies continued to arrive, take notes, and achieve nothing—a service for which Township residents paid approximately $2.3 million annually in taxes to Washtenaw County.
“What do we get for that $2.3 million?” a resident had asked, at a board meeting.
“Regional law enforcement services,” Peb Stumbles had replied.
“But they don’t do anything.”
“They respond to calls.”
“And then they don’t do anything.”
“That’s a matter for the Sheriff’s Office, not the Township.”
“But we’re paying the Sheriff’s Office.”
“Through the County. You’d need to take that up with them.”
“How?”
“I’m sure there’s a process.”
There was a process. The process involved attending Washtenaw County Board meetings, which occurred on the first and third Wednesdays of each month at 6:30 PM in Ann Arbor—a thirty-minute drive for most Township residents, assuming traffic cooperated, which it did not.
No one attended.
The system continued.
The Animal Control question was, if anything, more elegant in its dysfunction.
Ypsilanti Township had once employed an Animal Control officer. His name was Dave. Dave had a truck with a cage in the back and a genuine affection for creatures that bit him. Dave responded to calls about loose dogs, feral cats, and one memorable incident involving an escaped emu that had wandered down Michigan Avenue with the confidence of a tenured professor.
Then the township did the math.
“Dave costs $47,000 a year,” said Peb Stumbles, reviewing the budget at a meeting attended by herself, the board, and Gerald.
“Dave also handles approximately 400 calls annually,” said a board member who had not yet learned that context was unwelcome.
“But what if—and hear me out—we simply didn’t have Dave?”
“What would happen to the animal calls?”
“The Sheriff’s Office can handle them.”
“Can they?”
“They handle everything else.”
This was technically true, in the same way that a sieve “handles” water.
The motion passed 5-0. It was not a controversial vote. Nothing was controversial when there was no opposition—on the ballot, in the room, or in concept.
Dave was offered a position with Ann Arbor at reduced pay. He took it. The emu situation was declared “resolved” on the grounds that no one had seen the emu in several weeks. (The emu had, in fact, established residence in a ravine near Ford Lake, where it would live comfortably for six more years, occasionally startling joggers.)
In Dave’s absence, animal complaints were routed to the Washtenaw County Sheriff’s Office, which handled them with the same vigor it applied to all Township matters.
“There’s a dog loose in my yard,” a resident would report.
“Is the dog currently attacking you?”
“No, but—”
“Is the dog rabid?”
“I don’t—how would I—”
“Call back if the situation escalates.”
Click.
The situation, invariably, would escalate. The dog would leave. Another dog would arrive. The cycle would continue. Residents learned to coexist with roaming animals in the same way medieval peasants had learned to coexist with wolves—through vigilance, folklore, and a resigned acceptance that the castle wasn’t sending anyone.
“You could run for Township Supervisor,” someone suggested once, to a resident who had complained particularly loudly about the animal situation.
“Against Peb Stumbles?”
“Against whoever’s on the ballot.”
“Peb Stumbles is the only one on the ballot.”
“So you’d be the second one.”
The resident considered this. Running for office would require collecting signatures, filing paperwork, attending forums, and explaining to voters why they should choose him over an incumbent who had held the position for seventeen years and who had, by virtue of never facing opposition, never been required to defend a single decision.
“I don’t have time for that,” the resident said.
“Neither does anyone else.”
And so Peb Stumbles remained, year after year, the only name on a ballot that most residents didn’t know existed, for a position that most residents couldn’t define, in an election that most residents didn’t realize was happening until it had already happened.
Democracy, in Ypsilanti Township, was a technical term.
That night, at Al-Kareem’s—amid the garbage that had begun to develop its own political consciousness—seventeen families gathered for what would later be called either the First Continental Congress of Zebsilanti or “that time Baba got too into it,” depending on who was telling the story.
“We pay taxes,” said Omar Haddad, who owned the cell phone repair shop. “For what?”
“Protection,” someone offered.
“From whom? The deputies?”
A bitter laugh circled the room. Everyone had a Deputy VanDamn story. Mariam Khalil’s had involved a break-in, a stolen laptop, and a report that described the perpetrator as “unknown individual(s), possibly male, possibly not.” Yusuf Nasser’s had involved a hit-and-run, three witnesses, a license plate number, and a follow-up call six weeks later informing him the case was “administratively closed due to lack of leads.”
“The leads were on the form,” Yusuf had said.
“I don’t see any leads,” the deputy had replied, not looking at the form.
“Recycling,” someone else offered now, with evident sarcasm.
“Every other week!”
“My garage looks like an Amazon fulfillment center.”
“I’ve started burning the cardboard.”
“That’s illegal.”
“So is letting it pile up until it becomes a fire hazard. Pick your crime.”
“We could vote for someone else,” suggested Mariam, without conviction.
“There is no one else. There’s never anyone else. It’s been Peb Stumbles since I moved here.”
“It’s been Peb Stumbles since before you moved here.”
“It’ll be Peb Stumbles after we’re all dead.”
“Has anyone tried running against her?”
A silence fell over the room. It was the silence of people who had not tried, who had not considered trying, who had accepted the single-name ballot as a fact of nature rather than a failure of civic participation.
“Why would you?” Farid said finally. “What would you even run on? ‘I’ll do things differently’? She’s never had to explain what she does. There’s no record to run against. There’s no platform to oppose. There’s just… Peb Stumbles. Forever. Like the water tower.”
“Infrastructure,” someone else offered, trying to return to the original question.
“What infrastructure?”
A silence fell over the room. Outside, a pothole that had been reported fourteen times consumed a Kia Sportage up to its wheel wells. No one noticed. This was simply how Kias existed now.
“We could secede,” said Rania Mansour, Farid’s daughter, who was sixteen and had just finished a unit on self-determination in AP World History.
Everyone laughed.
“No, listen,” she said, and unfolded a map she’d printed at the library. “The township already sort of seceded from Ypsilanti proper. There’s the city, there’s the township—it’s confusing on purpose. No one knows who’s responsible for what. That’s how Peb Stumbles stays in power—no one can figure out what she’s supposed to be doing, so no one can prove she’s not doing it.”
“Is that how secession works?”
“It’s how this works,” she replied. “This is Michigan. Half the municipalities exist because someone got mad about snow plowing in 1973. We’re just… continuing the tradition. We just need a declaration, a flag, and a name.”
“And what about police?” asked Omar.
“What about police?” Rania replied. “We’re already not getting police. At least this way we stop paying for the privilege.”
“And recycling?”
“Weekly,” Rania said firmly. “If we’re doing this, we’re doing it right.”
“And elections?”
“Contested elections. Multiple candidates. Actual choices. Like a democracy.”
The room fell silent. It was the silence of people confronting an argument they could not refute—and the promise of contested elections, which felt almost utopian.
The naming committee convened immediately.
The original suggestion was “New Homs,” which was vetoed by the Syrian faction for being “too on the nose” and by the Palestinian faction for being “not on the nose we wanted.” “Little Ramallah” was proposed and tabled. “Township of Actual Functioning Services” received three votes but was deemed “too aggressive.”
Then young Khaled Bazzi, who was seven and should have been in bed, pointed out the window toward the Ypsilanti water tower—that magnificent 147-foot brick monument to Victorian engineering, which had graced postcards, t-shirts, and one particularly memorable bachelorette party banner with the slogan “YpsiLANTI IF YOU KNOW WHAT I MEAN.”
“It looks like a zubb,” he said, using the Arabic word.
“Khaled,” his mother hissed.
But the damage was done. The adults stared at the tower with fresh eyes. It had stood since 1890, intended by its architects as a symbol of civic progress. It was 85 feet of brick shaft topped by a 35-foot ornamental cap. It had been on the National Register of Historic Places since 1981.
It was absolutely, unmistakably, phallic.
“Zebsilanti,” said Omar slowly. “Zubb-silanti.”
“That’s terrible,” said Farid.
“It’s perfect,” said Rania.
The vote passed 14-3, with three abstentions from residents who felt the whole thing had gotten away from them.
The Declaration of Independence of the Glorious Republic of Zebsilanti was ratified on a Tuesday, printed on a laser printer with a “LOW TONER” warning, and posted to the township’s official Facebook page, which had 340 followers and had last been updated to announce a rabies clinic in 2019.
The document read, in part:
“When in the course of human events, it becomes necessary for a people to dissolve the political bands which have connected them to a governance structure that cannot collect trash but can absolutely fine you for dandelions, a decent respect for the opinions of mankind requires that they should declare the causes which impel them to separation. These causes are as follows:
- We have been ticketed for grass.
- We have not been protected from crime.
- We have paid for Sheriff’s deputies who arrive, take notes, and achieve nothing.
- Our Animal Control officer was eliminated to save $47,000, which is coincidentally the exact cost of the Township Supervisor’s ‘conference travel’ budget.
- Our recycling is collected every other week, which is not how Amazon deliveries work.
- Our garbage has achieved sentience and is now a voting bloc—which means it has more electoral choices than we do.
- We have been governed for seventeen years by a single person who has never faced opposition, never explained her platform, and never been required to justify a single decision to voters who had no alternative.
- Gerald.
We therefore declare ourselves a free and independent republic, subject only to the laws of hospitality, the authority of our mothers, and the zoning regulations we will write ourselves and actually enforce consistently. Our elections will feature multiple candidates. Our recycling will be weekly. Our ballots will contain more than one name.
We have seen what single-name democracy looks like.
We choose otherwise.”
The township’s response was swift and bureaucratic. A Notice of Ordinance Violation was issued for “unauthorized signage” when residents erected a border checkpoint consisting of two traffic cones and a card table offering complimentary hummus to all who recognized Zebsilanti sovereignty.
The notice was received, laminated, and displayed in the newly established National Museum of Zebsilanti, which was the back room of the cell phone repair shop. It was labeled: “FIRST ACT OF FOREIGN AGGRESSION.”
A Sheriff’s deputy was dispatched to investigate. He arrived three hours later, took notes, and filed a report that read: Signage present. Hummus offered. Civil matter. No action required.
Peb Stumbles issued a statement through the Township’s official channels (a mimeographed flyer placed in the lobby of the Township offices, which were open from 9 AM to 3 PM on weekdays, excluding lunch):
“The Township does not recognize the legitimacy of so-called ‘Zebsilanti.’ Residents are reminded that all ordinances remain in effect and that failure to comply may result in citations. The Township remains committed to serving all residents through our regional approach to governance.”
The statement did not address any of the specific complaints raised in the Declaration. It did not need to. In seventeen years, Peb Stumbles had never been required to address specific complaints, because specific complaints required specific responses, and specific responses could be criticized, and criticism required an opponent, and opponents did not exist.
“Regional approach to governance” remained undefined.
The mimeograph was added to the National Museum, labeled: “RESPONSE FROM THE OCCUPIED GOVERNMENT.”
PART TWO: CONSOLIDATION
The Republic’s first year was marked by unprecedented achievements.
A sanitation department was established, consisting of two guys named Mahmoud with a pickup truck. Garbage collection became weekly, reliable, and accompanied by a brief assessment of whether your recycling technique was “disappointing your mother.” Compliance was absolute.
More revolutionary still: recycling became weekly. The Mahmouds collected cardboard, glass, and plastic every seven days without fail. Within a month, garages across Zebsilanti were reclaimed from their cardboard prisons. Residents wept. One man discovered he had a workbench. He had forgotten.
“I haven’t seen this much floor space since 2019,” said Yusuf Nasser, standing in his garage with the expression of a man who had been liberated from forces he hadn’t realized were occupying him.
The Mahmouds also instituted a policy of “active recycling consultation,” which meant they would knock on your door if your recycling was contaminated. This was technically optional, but the knock carried the weight of community judgment, and no one wanted to be the person who didn’t know that pizza boxes with grease stains weren’t recyclable.
A police force was deemed unnecessary after the community adopted what Rania called “the Palestinian Grandmother Protocol,” whereby any suspicious activity was immediately reported to a rotating council of elderly women who would appear at the offender’s door with tea, cookies, and a comprehensive inventory of their sins dating back to childhood. Crime dropped 94%. The remaining 6% was committed by outsiders who didn’t understand that Mrs. Haddad had sources.
“How does she know?” a would-be package thief was heard to ask, trembling, as Mrs. Haddad recounted his 2003 shoplifting incident at a Kroger in Belleville. “How does she know?”
She knew because she knew. That was the system. It was better than Box 14-C.
Landscaping ordinances were reformed under the principle of “Ya’ani, It Depends.” Grass could be whatever height suited the homeowner, unless it was attracting vermin, in which case a neighbor would say something directly like a normal person instead of photographing it from a minivan. Violations were adjudicated by a council of aunties who weighed factors such as: Was the homeowner elderly? Going through something? Recently widowed? Had they brought food when your father was sick? The system was arbitrary, opaque, and somehow achieved perfect justice.
Most revolutionary of all: Zebsilanti held its first election.
The position was Rotating Council Chair—a largely ceremonial role that involved moderating Thursday meetings and deciding when the baklava had run out. But the principle was important. The ballot contained three names.
Three.
Residents stared at their ballots with something approaching wonder.
“I don’t understand,” said one elderly woman. “Which one is the real candidate?”
“They’re all real,” Rania explained gently.
“But which one is supposed to win?”
“Whichever one you choose.”
The woman looked at the ballot for a long moment. Then she began to cry.
“I haven’t chosen anything in seventeen years,” she said.
The election was won by Omar Haddad, who received 412 votes. The second-place candidate received 287. The third received 103. There were twelve write-in votes for “Anyone But Peb Stumbles,” which were counted as valid expressions of democratic sentiment.
The economy flourished. The national currency, the Zubb (exchange rate: 1 Zubb = $1.05 or one falafel sandwich, whichever the vendor preferred), was backed by a reserve of goodwill, community trust, and a truly unreasonable amount of olive oil stored in the basement of the mosque.
International recognition remained elusive, though a confused functionary at the United Nations did accidentally forward Zebsilanti’s membership application to the Committee on Decolonization, where it was placed in a pile labeled “PENDING” that had not been reviewed since 1987.
PART THREE: THE FIRST CONSTITUTIONAL CRISIS
The first constitutional crisis occurred in Year Two, when Gerald returned.
He appeared at the border checkpoint on a gray November morning, clipboard in hand, measuring tape at his belt, cargo shorts somehow persisting despite temperatures that demanded otherwise. He presented credentials from Ypsilanti Charter Township identifying him as a “Code Compliance Liaison” empowered to assess properties within “disputed administrative zones.”
The border guard—sixteen-year-old Layla Haddad, who was working the checkpoint for community service credit—examined the documents with the gravity of a customs official at a Cold War crossing.
“Purpose of visit?”
“Official business.”
“Specific nature of business?”
“Assessment of vegetation and structural compliance.”
Layla stamped his papers with a stamp she had bought on Amazon that said “RECEIVED” in red ink. It had no legal significance but looked extremely official.
“You may enter the Glorious Republic,” she said. “Please note that our ordinances differ from those of the occupied territories. Grass may be any height. Political expression via lawn signage is protected. And if you cite anyone for anything, my grandmother will find out.”
Gerald hesitated.
“She has sources,” Layla added.
“I have authority from the Township Supervisor—”
“Which Township Supervisor? The one who’s been on the ballot alone for seventeen years? The one no one voted for because there was no one else to vote for?” Layla smiled pleasantly. “We have elections here, sir. Real ones. With choices. Your authority isn’t recognized.”
Gerald stared at her.
“Also,” Layla continued, “my grandmother would like you to know that she remembers when you cited Mr. Mansour for his grass while ignoring the abandoned car on Prospect Street. She has questions about your enforcement priorities.”
Gerald turned around and left.
The event was commemorated annually thereafter as Victory Day, celebrated with a parade down Michigan Avenue (the 0.3-mile stretch that constituted Zebsilanti’s sovereign territory) and a ceremonial burning of a cargo shorts effigy stuffed with obsolete ordinance documents.
PART FOUR: THE Ben LAVEN AFFAIR
Or: The People vs. Four Dogs and the Idiot Who Enabled Them
A Case Study in Domestic Terrorism (Noise Division)
The crisis that would test Zebsilanti’s founding principles—and establish precedents still debated in the Republic’s legal circles (which met Tuesdays at Al-Kareem’s, after the dinner rush)—began not with garbage or grass, but with noise.
Specifically: barking.
More specifically: the relentless, arrhythmic, neurologically corrosive barking of four dogs belonging to one Benjamin Laven, a resident of the disputed border zone between Zebsilanti and the occupied territories of Ypsilanti Charter Township.
The name would prove unfortunate.
Ben Laven—no relation, a coincidence of syllables that would haunt him—lived in a house that had once been beige and was now the color of resigned neglect. The property, which Marwan Jaziri would later describe in his formal complaint as “the compound,” featured a picket fence, perpetually drawn blinds, and a yard that appeared to have been landscaped by entropy itself.
From this compound, four dogs conducted what can only be described as a sustained campaign of psychological warfare against the surrounding population.
The dogs were:
1. Nutslam, a geriatric Golden Retriever who served as the cell’s spiritual leader. Nutslam was blind, senile, and produced a bark that defied acoustic explanation—a strangled, agonized howl that sounded, according to Marwan’s formal complaint, “as though his scrotum had been caught in the door of an F-150 that subsequently drove off, leaving him to vocalize his trauma in perpetuity.” Nutslam barked at nothing, because Nutslam could see nothing. He barked at sounds, at smells, at vibrations in the earth, at memories of things that may or may not have happened. He barked, it seemed, at the very concept of existence, and found it wanting.
2. Skunk, a black-and-white Pomeranian who functioned as the cell’s reconnaissance unit. Skunk’s coloring was such that, from a distance, he appeared to be an actual skunk, prompting at least three neighbors to call the (nonexistent) Animal Control about a “rabid skunk” before realizing the skunk was, in fact, a dog. Skunk’s bark was high-pitched and staccato, a machine-gun burst of indignation that he deployed at anything that moved and several things that didn’t. He had once barked at a garden hose for forty-five minutes. The hose had not moved. Skunk remained vigilant.
3. Minion, a jet-black Pomeranian who served as the cell’s psychological operations unit. Minion’s bark was not, technically, a bark—it was a shriek, a scream, a sound that Marwan’s veterinary behaviorist consultant described as “what I imagine a bird would sound like if it were feasting on Prometheus’ liver while Prometheus was still using it.” The sound was high, sustained, and somehow wet, as though Minion were gargling his own fury. Minion weighed six pounds. Minion produced enough noise for sixty.
4. Bo, a young female Golden Retriever who had, by all accounts, been a normal dog before her exposure to the Ben Laven compound. Bo had arrived as a puppy, friendly and quiet, the kind of dog that neighbors smiled at. Within six months, she had been fully radicalized. Bo now barked whenever the others barked, a convert to the cause, a true believer who had learned that this was simply what dogs did. Her bark was the saddest of all—the bark of a dog who could have been good, who had been good, but who had been failed by circumstance and leadership.
“It’s like living next to a terrorist training camp,” Marwan Jaziri had said once, in the early days, before he understood how apt the comparison would become. “Except the terrorists are dogs and their leader is a blind, senile Golden Retriever whose bark sounds like testicular catastrophe.”
The cell operated in shifts, maintaining a continuous barking presence that military strategists would later recognize as a classic “harassment and interdiction” pattern:
0500-0800: Nutslam’s dawn patrol. Unable to see the sunrise, he barked at it anyway, his anguished howl serving as an alarm clock for a three-block radius. The sound built slowly, a moan becoming a wail becoming a full-throated scream of existential confusion. Residents learned to wake before Nutslam, if only to brace themselves.
0800-1200: Skunk assumed primary barking duties, responding to pedestrians, vehicles, mail carriers, leaves, shadows, and on one memorable occasion, his own reflection in a puddle. The puddle incident lasted two hours.
1200-1400: Reduced activity. Even terrorists need lunch.
1400-1800: Minion’s shift. The Prometheus hours, residents called them. Minion would position himself at the fence and emit his liver-eating-bird shriek at anything that passed. Children walking home from school learned to cross the street. Adults did too.
1800-2200: Full cell activation. Dinnertime triggered a coordinated assault, all four dogs barking in overlapping waves that created a wall of sound impenetrable to human thought. Conversations stopped. Televisions were turned up, then up further, then muted in defeat. Residents ate in silence, chewing grimly, waiting for 10 PM.
2200-0500: Bo’s night watch. The youngest member of the cell, Bo had been assigned the overnight shift, barking at raccoons, possums, and the occasional car with the enthusiasm of a new recruit eager to prove herself. She was good at it. She had learned from the best. Or the worst. It was hard to tell the difference.
Intelligence Assessment: The Ben Laven Compound
The Zebsilanti Intelligence Community (Mrs. Haddad, primarily, supplemented by her network of sources) compiled the following assessment of the Ben Laven operation:
Subject: Benjamin “Ben” Laven
Status: Person of Interest (Noise Crimes)
Known Associates: Four unlicensed canines (see attached profiles)
Threat Level: Elevated (Sleep Deprivation Division)
Organizational Structure:
Analysis indicates a decentralized command structure with Nutslam serving as ideological leader despite (or perhaps because of) his apparent cognitive decline. His blindness and senility have not diminished his authority; if anything, they have enhanced it, lending his bark an oracular quality that the other dogs appear to interpret as divine instruction.
Skunk and Minion function as operational commanders, coordinating daytime harassment activities. Bo represents the most concerning development: evidence of successful recruitment and radicalization of a previously moderate asset.
Assessment:
The Ben Laven cell represents a persistent, low-intensity threat to regional stability. Unlike traditional noise nuisances, which respond to intervention, the Ben Laven dogs appear ideologically committed to their campaign. Nutslam’s continued leadership despite obvious impairment suggests a cult-like devotion among cell members.
Ben Laven himself presents as either a passive supporter or a useful idiot—providing material support (food, shelter) without direct involvement in operations. His repeated claims of ignorance (“I didn’t know they were that loud”) are assessed as either genuine obliviousness or strategic denial. The fact that he can sleep through Nutslam’s 5 AM testicular aria suggests either profound hearing loss or profound indifference. Both are concerning.
Recommended Action:
Continued monitoring. Formal complaint process has proven ineffective (see: 35 filed complaints, 0 enforcement actions). Alternative approaches under consideration.
The Chronicle of Complaints: A Documentary Record
Marwan Jaziri was an accountant. He believed in systems. He believed that problems had solutions, that authorities existed to provide those solutions, and that documentation was the bridge between grievance and resolution.
He was about to learn otherwise.
Complaint #1 (March 15, Year 1)
Method: Phone call to Washtenaw County Animal Control
Response: “Animal Control services for your area have been discontinued. For noise complaints, contact the Sheriff’s Office.”
Complaint #2 (March 16, Year 1)
Method: Phone call to Washtenaw County Sheriff’s Office
Response: “Is the dog currently attacking someone?”
“No, but—”
“Barking is not an emergency. This is a civil matter.”
Click.
Complaint #3 (March 22, Year 1)
Method: Written letter to Ypsilanti Charter Township
Response: Form letter (received April 14): “Thank you for your concern. Your matter has been referred to the appropriate department.”
The appropriate department was never identified. Marwan suspected it did not exist, like the weapons of mass destruction that had justified other interventions in other compounds belonging to other men with similar names.
Complaint #4 (April 3, Year 1)
Method: Phone call to Washtenaw County Sheriff’s Office (Non-Emergency Line)
Response: A deputy would be dispatched to “assess the situation.”
Deputy Marcus VanDamn arrived four hours later. The dogs had briefly stopped barking because Nutslam had walked into a wall and was taking a moment to recalibrate.
Report filed: Responded to noise complaint. No excessive noise observed upon arrival. One dog appeared confused. Unfounded.
Marwan had begun to understand that the Ben Laven compound operated like any effective cell: it went quiet when authorities approached, then resumed operations the moment they left. The dogs had not been trained to do this. They had simply evolved the behavior through natural selection—the selection pressure being Deputy VanDamn’s four-hour response time.
Complaint #5 (April 4, Year 1)
Method: Phone call to Washtenaw County Sheriff’s Office with video evidence
Response: “We don’t accept video submissions. A deputy can be dispatched to observe.”
“But I have evidence. Right here. On my phone. I can email it.”
“Sir, our system doesn’t—”
“It’s on YouTube. I can send you a link. It’s titled ‘THE BEN LAVEN COMPOUND DAY 47.’ You can hear a dog that sounds like his genitals were—”
“Sir, I’m going to stop you there.”
Complaint #6 (April 10, Year 1)
Method: Attendance at Ypsilanti Township Board Meeting, 4:30 PM
Result: Marwan took half a day off work to attend. He was the only member of the public present. Peb Stumbles presided. The agenda included approval of minutes, budget amendments, and “public comment.”
“I’d like to discuss the noise ordinance enforcement,” Marwan said, when called upon.
“You have three minutes,” Peb Stumbles said, starting her stopwatch.
Marwan spoke for two minutes and forty-seven seconds, describing the situation in detail.
“Your time is nearly up,” Peb Stumbles said.
“I have thirteen seconds left.”
“Noted. Is there a question?”
“What is the Township doing about noise complaints?”
“That’s a matter for the Sheriff’s Office.”
“But the Township contracts with the Sheriff’s Office. Don’t you have any oversight?”
“We have a regional approach to public safety.”
“What does that mean?”
“It means the Sheriff’s Office handles enforcement.”
“And if they don’t enforce anything?”
“Your three minutes are up.”
The meeting moved to budget amendments. Marwan left. Nothing changed.
Complaints #7-35 (April, Year 1 – June, Year 2)
Method: Everything available
Response: A vast taxonomy of bureaucratic deflection, including: “This is a civil matter” (17 times), “You’ll need to contact the Township” (8 times, from the Sheriff’s Office), “You’ll need to contact the Sheriff’s Office” (6 times, from the Township), “Have you considered mediation?” (3 times, with no mediator ever provided), “The noise ordinance requires sustained measurement by a certified technician” (once, with no technician available within 60 miles), “Supervisor Stumbles is not available for comment” (4 times), and “That falls outside our jurisdiction” (12 times, from entities that seemed to have overlapping jurisdiction with everyone and responsibility for nothing).
Complaint #35 (June 14, Year 2)
Method: Formal noise complaint with 114 pages of documentation, including audio recordings, video evidence, a decibel log maintained over 90 days, photographs of the dogs, photographs of Ben Laven ignoring the dogs, a spectrographic analysis of Minion’s bark proving it exceeded frequencies typically produced by terrestrial mammals, and a notarized statement from a veterinary behaviorist who had observed (from a distance) that Nutslam displayed “symptoms consistent with advanced cognitive decline” and should “probably be evaluated for quality of life concerns, although I say this based solely on the sound he makes, which is upsetting.”
Response: The complaint was rejected for “improper formatting.” The proper format was not specified. The complaint was invited to be resubmitted.
Marwan submitted a public records request for the proper format. The response, received six weeks later, was a single page that read: “Complaints should be submitted in proper format.”
The Breaking Point
On the morning of June 15, Year 2, Marwan Jaziri had not slept in thirty-one hours.
The dogs had barked through the night. Nutslam had begun his aria at 4:47 AM—thirteen minutes early, a deviation that somehow made it worse, as if even the schedule of suffering had become unreliable. The sound had started as a moan, risen to a howl, and peaked at what Marwan could only describe as “the noise a soul makes when leaving a body that was not ready to release it.”
Skunk had joined in at 5:15, his staccato yapping providing a percussive counterpoint to Nutslam’s melody of despair.
Minion had contributed his liver-eating-bird shriek at 5:30, adding a high harmonic that made Marwan’s sinuses ache.
And Bo—poor, radicalized Bo—had tied it all together, her bark the steady rhythm section of a band no one had asked to hear.
At 6:30 AM, Ben Laven had emerged in his bathrobe, scratched himself, and said the words that had become a kind of dark mantra in the neighborhood: “Keep it down, guys.”
The dogs had ignored him.
They always ignored him.
He had gone back inside.
Marwan stood at his window and watched the door close.
Something in Marwan Jaziri—accountant, believer in systems, compiler of 114 pages of documentation that no one had read—broke.
Or perhaps it didn’t break. Perhaps it simply reorganized.
He had tried diplomacy. He had tried the proper channels. He had attended a 4:30 PM meeting and been given three minutes and no answers. He had tried everything a reasonable person was supposed to try, and he had been ignored, dismissed, and ultimately reported to the very authorities who had failed to help him.
The system had failed.
It had failed, in fact, exactly as it was designed to fail—to diffuse responsibility across so many entities that no single entity could be held accountable, to create processes that existed not to solve problems but to exhaust the people who reported them, to maintain the appearance of governance without the inconvenience of actually governing.
Peb Stumbles had been Township Supervisor for seventeen years. In that time, she had never faced an opponent, never defended a decision, never been required to explain why residents paid for services they didn’t receive. She existed in a perfect equilibrium of non-accountability—the single name on a ballot that no one knew existed, presiding over meetings that no one could attend, issuing statements that explained nothing.
The system had failed because the system was designed to fail.
It was time for direct action.
The Capture
The following account is reconstructed from witness statements, surveillance footage from Mrs. Haddad’s Ring doorbell (which captured a partial view of the Ben Laven property), and Marwan’s own testimony before the People’s Tribunal.
At approximately 7:15 AM, Marwan Jaziri crossed into the disputed border zone carrying: one roll of duct tape, four dog treats (bacon-flavored, high-value), one legally purchased dog whistle, one Bluetooth speaker playing a frequency designed to calm anxious canines (purchased from Amazon, $34.99, 3.5 stars), one copy of the Washtenaw County noise ordinance (highlighted), and one copy of the Geneva Convention (also highlighted, for reasons that would become clear).
He approached the Ben Laven property. The dogs reacted according to their natures:
Nutslam barked at nothing, because he couldn’t see Marwan approaching. Skunk barked directly at Nutslam. Minion produced his signature shriek, which Marwan had learned to endure through a combination of earplugs and spite. Bo barked because the others were barking.
Then Marwan produced the treats.
The barking stopped.
All four dogs—even Nutslam, who had smelled the bacon through the fog of his senility—fell silent and sat down.
Marwan gave them the treats.
The dogs had never, to his knowledge, been rewarded for silence. They had never been rewarded for much of anything except for barking. They accepted the treats with the confused gratitude of prisoners offered an unexpected kindness.
“Good dogs,” Marwan said.
Nutslam’s tail wagged. He couldn’t see Marwan, but he could hear kindness in the voice, and perhaps that was enough.
Then Marwan knocked on Ben Laven’s door.
What happened next was described in Deputy VanDamn’s report as: Complainant alleges unlawful detention. Alleged perpetrator disputes characterization. No injuries. Civil matter. Unfounded.
What actually happened was this:
Marwan Jaziri invited Ben Laven to “discuss the situation” in Marwan’s backyard, which had been prepared overnight. Ben Laven, who had never considered Marwan a physical threat (correctly) and who was genuinely confused about why his neighbor seemed so upset (incorrectly), agreed.
He brought the dogs.
This was his mistake.
Marwan’s backyard had been transformed. A card table had been erected, draped in a bedsheet that Marwan’s wife had tie-dyed for a 2019 charity event and which now served as the flag of an ad hoc judiciary. Three chairs had been arranged behind the table. A single chair faced them—the defendant’s position. And four dog crates, borrowed from the Zebsilanti community center’s emergency pet supplies, had been arranged to the side.
A hand-painted sign hung above the table. It read: THE PEOPLE’S TRIBUNAL FOR CRIMES AGAINST SLEEP.
Below it, in smaller letters: “Justice Delayed Is Justice Denied — Also, Your Dogs Are Too Loud”
“What the hell is this?” Ben Laven asked.
“This,” said Marwan, “is a tribunal.”
“A what?”
“You are being charged with crimes against the peace and sanity of the Zebsilanti border region. Your co-defendants”—he gestured at the dogs—”are charged as accomplices. Except Bo, who is being charged as a victim of radicalization.”
Bo wagged her tail. She didn’t understand the words, but she understood that someone was paying attention to her, which was more than Ben Laven typically provided.
“This is insane.”
“This is due process,” Marwan replied. “Something you have been shielded from by the systematic failures of Washtenaw County and Ypsilanti Charter Township—whose Supervisor, I should note, has been the only name on the ballot for seventeen consecutive years, during which time exactly nothing has improved. In the absence of legitimate authority, the people must act.”
He paused, then added: “Also, I want to be clear that this is entirely nonviolent. The Geneva Convention—” he held up his highlighted copy “—applies. You are being treated humanely. There is coffee.”
There was, in fact, coffee. Mrs. Haddad had brought it. She had also brought cookies, because no proceeding in Zebsilanti could occur without refreshments, even one that was technically an extrajudicial detention.
“I’m leaving,” Ben Laven said.
“You are not.”
“You can’t keep me here.”
“I am not keeping you anywhere. You are free to leave at any time. However, if you leave, this tribunal will proceed in absentia, and its findings will be published in the Zebsilanti Gazette”—a newsletter Marwan had founded that morning, circulation: 47—”and posted to the Ypsilanti Township Community Facebook group, which has 8,400 members.”
Ben Laven hesitated.
“The post will include the video compilation,” Marwan added. “All fourteen hours. Titled, I should mention, ‘THE BEN LAVEN COMPOUND: A DOCUMENTARY.’ There’s a whole section on Nutslam. I’ve had to put viewer discretion warnings on it because of the sound he makes.”
“The sound he—”
“You know the sound. Everyone knows the sound. It’s the sound of testicular tragedy, Ben. It’s the sound of a dog whose body has betrayed him and who has chosen to narrate that betrayal at 5 AM every morning for six years. It’s upsetting. And 8,400 people are going to hear it, and they’re going to have questions.”
Ben Laven sat down.
In his crate, Nutslam let out a low moan—not a bark, just a moan, the sound of an old dog settling into unfamiliar comfort. It was still unpleasant. But it was quieter.
The Tribunal
The three judges arrived over the next hour, summoned by a group text that read: Ben Laven situation escalating. Need witnesses. Bring coffee.
The judges were:
1. Mrs. Haddad, representing the Council of Grandmothers and serving as Chief Justice. She had sources. She always had sources. She had also not slept well in twenty-six months, and her sources had confirmed that neither had anyone else within a three-block radius of the Ben Laven compound.
2. Omar Haddad, representing the Zebsilanti business community, which had received numerous complaints about barking disturbing customers at the cell phone repair shop. “People are trying to explain their cracked screens,” he had said. “They can’t hear themselves think. Especially when the black one does that noise.”
3. Rania Mansour, now nineteen, serving as Recording Secretary and Constitutional Scholar. She was taking notes for her thesis, which had expanded to include a chapter on “Community-Based Justice in the Absence of Functional Institutions.”
The prosecution was conducted by Marwan himself, who had prepared a 47-slide PowerPoint presentation titled “THE CASE AGAINST BEN LAVEN: A COMPREHENSIVE ANALYSIS OF NEGLIGENCE, NUISANCE, AND THE BANALITY OF INDIFFERENCE.”
The subtitle read: “Or: How One Man’s Incompetence Became Everyone’s Problem.”
The defense was conducted by Ben Laven, who had not prepared anything and kept asking if he could call a lawyer.
“You may call anyone you wish,” Mrs. Haddad said. “This tribunal has no power to prevent you from doing so. It also has no power to compel you to stay. And yet—here we are.”
Ben Laven did not call a lawyer. He did not call anyone. He sat in his chair, increasingly aware that he was outnumbered by people who had also heard his dogs for six years and who were looking at him with the quiet, exhausted disappointment of a community that had run out of patience.
Selected Proceedings
PROSECUTION EXHIBIT A: Audio Compilation
Marwan played seventeen minutes of continuous barking, recorded between 2 AM and 4 AM on a Tuesday.
The tribunal listened in silence.
Nutslam’s portion—a sustained, wavering howl that seemed to contain within it all the sorrow of a creature who had outlived his understanding of the world—prompted Mrs. Haddad to close her eyes and whisper something that might have been a prayer.
Minion’s contribution caused Omar to physically recoil. “What is that?” he asked.
“That,” Marwan said, “is Minion. He’s a Pomeranian. Six pounds. Sounds like a bird eating a titan’s liver.”
“That’s… very specific.”
“I’ve had six years to think about it.”
“I was asleep,” Ben Laven said, when the recording ended.
“Yes,” Marwan replied. “You were. We were not.“
PROSECUTION EXHIBIT B: Decibel Readings
Average sustained noise level: 87 decibels. Peak readings (during Minion’s shifts): 94 decibels. For comparison: a chainsaw produces 100 decibels. OSHA recommends hearing protection for sustained exposure above 85.
“These readings were taken from inside my house,” Marwan noted. “With the windows closed. Minion alone exceeded safe workplace exposure limits. Minion weighs six pounds.“
PROSECUTION EXHIBIT C: The Radicalization of Bo
Marwan presented a timeline with photographs.
“This is Bo when she arrived at the Ben Laven compound, eighteen months ago.”
The photograph showed a puppy, tail wagging, eyes bright, mouth closed.
“This is Bo six months later.”
The photograph showed a dog mid-bark, eyes wide, posture tense.
“This is Bo now.”
The photograph showed a dog who had fully integrated into the cell—barking alongside the others, her original personality subsumed into the collective.
“Bo was not born a problem,” Marwan said. “Bo was made a problem. She learned to bark constantly because that’s what the other dogs did, and no one taught her otherwise. She was radicalized, Your Honors. Radicalized by neglect, by the absence of leadership, by an environment that normalized extremism.”
“You’re making her sound like a terrorist,” Ben Laven said.
The room fell silent.
“I am making her sound like a victim,” Marwan replied carefully. “A victim who has become a perpetrator through no fault of her own. If the comparison to other forms of radicalization seems apt, perhaps you should consider why.”
In her crate, Bo whined softly. She had been given a treat. She had been spoken about with something like sympathy. She was confused, but she was also, for the first time in months, quiet.
PROSECUTION EXHIBIT D: The Dogs Themselves
The four dogs were brought before the tribunal in their crates.
Nutslam stared at nothing, his clouded eyes fixed on a point in space that may or may not have existed. He let out a low moan—not the full bark, just a preview, a trailer for the 5 AM feature presentation.
Skunk vibrated with barely contained fury, his black-and-white fur making him look, as always, like an especially aggressive skunk.
Minion opened his mouth and produced a sound that made Rania drop her pen. “Oh my God,” she said.
Bo sat quietly, looking at the judges, waiting for instruction. Of all the dogs, she seemed the most aware that something important was happening.
“These animals,” Marwan argued, “are not criminals. They are victims. Victims of an owner who has failed to provide adequate stimulation, training, or socialization. Nutslam is blind and senile, and yet he has received no veterinary evaluation, no cognitive support, no quality-of-life assessment. He paces the 25 square foot area inside the picket fence, confused, frightened, and he expresses that confusion and fear in the only way he knows how. The sound he makes, Your Honors—that sound is not aggression. It’s anguish. And Ben Laven has done nothing.”
“He’s just old,” Ben Laven said weakly.
“He’s old, and he’s suffering, and you’ve decided that his suffering is acceptable because addressing it would require effort. Skunk has been allowed to believe that everything is a threat because no one has shown him otherwise. Minion—” Marwan paused, searching for words. “Minion needs help. Professional help. The sound he makes is not normal. And Bo…” He looked at the young Golden Retriever, quiet in her crate. “Bo could have been a good dog. Bo was a good dog. And you let the others teach her to be this.”
Mrs. Haddad leaned forward. “Young man,” she said to Ben Laven, who was forty-seven, “do you know what I hear when that old dog makes that sound every morning?”
“No, ma’am.”
“I hear pain. I hear an animal who is suffering and confused. And I hear you, sleeping through it, because his pain is not your problem.” She paused. “My husband had dementia at the end. He would wake at night, confused, frightened. And I would wake with him, every time, because that is what you do when something depends on you. You do not sleep through their suffering. You attend to it.”
“They’re dogs—”
“They are lives you chose to be responsible for. And you have failed them. All of them. But especially the old one, who cannot see, who cannot understand, who can only feel—and what he feels is abandonment.” She settled back in her chair. “The compound is not the problem, Mr. Laven. You are the problem. The compound is merely where the problem lives.”
The Verdict
After forty-five minutes of deliberation (conducted over coffee and knafeh that Mrs. Bazzi had brought, because no Zebsilanti proceeding could occur without food), the tribunal delivered its verdict:
On the charge of Chronic Nuisance: Guilty.
On the charge of Negligent Animal Husbandry: Guilty.
On the charge of Indifference to Community Welfare: Guilty.
On the charge of Operating an Unsanctioned Noise Cell Within the Zebsilanti Border Region: Guilty.
On the charge of Permitting the Radicalization of a Previously Moderate Dog: Guilty.
On the charge of Allowing a Blind, Senile Dog to Suffer Without Veterinary Intervention: Guilty, with a recommendation for immediate action.
The dogs were found not guilty by reason of diminished capacity. “They’re dogs,” Omar explained. “They don’t know better. He was supposed to teach them.”
Nutslam was additionally found not guilty by reason of “clearly being unwell and deserving of compassion rather than blame.” A separate motion was passed expressing concern for his quality of life and recommending immediate veterinary evaluation.
Bo was found not guilty by reason of radicalization. “She was a good dog,” the verdict noted. “She can be a good dog again. With proper intervention.”
Minion was found not guilty but “deeply concerning.” The tribunal recommended a specialist evaluation.
Skunk was found not guilty but “extremely annoying.” The tribunal recommended training, and perhaps therapy for whatever made him believe that garden hoses were enemies.
The Sentence
The tribunal, having no actual legal authority, could not impose fines, imprisonment, or seizure of property. It could, however, impose social consequences, which in Zebsilanti were considerably more effective.
Ben Laven was sentenced to:
- Immediate veterinary evaluation for Nutslam, with particular attention to cognitive decline, pain management, and quality of life. “If that dog is suffering,” Mrs. Haddad said, “you will address it. One way or another.”
- Specialist consultation for Minion, to determine why a six-pound Pomeranian sounds like mythological torture.
- Mandatory enrollment in a dog training program, to be completed within 90 days. Progress reports would be submitted to the tribunal monthly. Bo was to be prioritized as “the most salvageable.”
- Daily walks of no less than 30 minutes per dog, even when it was cold, or hot, or rainy, or snowy. Every single day, to be verified by photographic evidence submitted to a community WhatsApp group created for this purpose. The group was named “Ben Laven Rehabilitation Watch.” It had 23 members within an hour.
- Soundproofing consultation, paid for by Ben Laven, to determine whether modifications to his property could reduce noise transmission to neighboring homes.
- Public acknowledgment of wrongdoing, in the form of a written letter to be posted in the Zebsilanti Gazette and read aloud at the next community gathering at Al-Kareem’s.
- Probation for the dogs, during which any resumption of excessive barking would result in the tribunal reconvening to consider “more creative remedies,” which were not specified but which Mrs. Haddad implied might involve her sources.
Ben Laven accepted the sentence.
He had no choice. The alternative was the Facebook post. And the audio-video compilation. And the fourteen-hour documentary featuring Nutslam’s testicular aria in full surround sound.
And Mrs. Haddad’s disappointment, which followed a man like weather.
Aftermath
Deputy VanDamn arrived at 2:47 PM, approximately six hours after Mrs. Haddad’s Ring doorbell had captured Marwan Jaziri escorting Ben Laven across property lines.
He took notes.
“So there was a… tribunal?” he asked.
“A community mediation session,” Rania corrected. “Entirely voluntary. Mr. Laven was free to leave at any time.”
“And the dogs?”
“Were provided treats, calming music, and more attention than they’ve received in six years. Nutslam fell asleep in his crate. I think it might be the first time he’s felt safe since he went blind.”
“I’ll need to include that in my report.”
“Please do. Box 14-C has room.”
Deputy VanDamn looked at his notepad. He had written: Tribunal? Dogs. Voluntary. Mediation. Testicular?
He crossed out the last word.
“So… no one’s pressing charges?”
“Against whom?” Marwan asked. “Mr. Laven, for six years of noise violations that your office declined to address? Or me, for hosting a neighborhood meeting in my backyard?”
“You could take this to the Township.”
“Which Township? The one run by Peb Stumbles? The one where she’s been the only name on the ballot since I was in high school?” Marwan smiled thinly. “We tried that. We tried everything. For six years. And here’s what we learned: Peb Stumbles doesn’t return calls. The Sheriff’s Office doesn’t enforce ordinances. Animal Control doesn’t exist. The only thing that works in Ypsilanti Township is the citation system for grass.”
Deputy VanDamn had nothing to say to this. It was, after all, true.
“So we built something that works,” Marwan continued. “It’s not official. It’s not recognized. It’s just… people, solving problems, because no one else will. That’s Zebsilanti. That’s what you’re looking at.”
The report, submitted the following week, read: Responded to complaint of unlawful detention. Upon investigation, determined to be community dispute resolution meeting. No evidence of coercion. All parties participated voluntarily. Refreshments provided. Dogs appeared comfortable. Civil matter. Unfounded.
It was the most accurate report Deputy VanDamn had ever filed.
Epilogue: The Ben Laven Reforms
The veterinary evaluation revealed that Nutslam was, in fact, suffering from untreated arthritis, cognitive dysfunction syndrome, and an ear infection that had likely been causing him pain for months. The pain, the vet explained, was probably why he barked the way he did—not out of malice, but out of discomfort, expressed the only way he knew how.
“You’re telling me,” Ben Laven said slowly, “that the sound he makes—”
“Is a pain response, yes. He hurts, Mr. Laven. He’s been hurting for a while.”
Ben Laven was quiet for a long moment.
“I didn’t know,” he said finally.
“You didn’t ask,” the vet replied, not unkindly. “But now you do.”
Nutslam was prescribed pain medication, anti-anxiety supplements, and a memory foam bed that Mrs. Bazzi insisted on purchasing because “that poor creature has suffered enough.” His barking reduced by 80%—not because he was silenced, but because he was no longer in pain.
The remaining barking was deemed acceptable. It was quieter. It was less anguished. It was the bark of an old dog who was, for the first time in years, comfortable.
Minion’s evaluation revealed that his shriek was related to excitement and frustration, compounded by the fact that no one had ever taught him any other way to express himself. A behaviorist worked with him for three months. He still made sounds that were somewhat upsetting, but they were shorter, less frequent, and no longer evoked Prometheus.
Skunk learned that not everything was a threat. This took longer. He remained vigilant, but his vigilance was now expressed through alert posture rather than forty-five-minute bark sessions at garden hoses. He still looked like a skunk. Neighbors no longer called Animal Control, primarily because Animal Control still didn’t exist.
Bo was the fastest rehabilitation. Once separated from the influence of the others, she remembered how to be a normal dog almost immediately. She stopped barking within weeks. She became, as the tribunal had predicted, a good dog.
She became, in fact, such a good dog that she was offered a position at the Zebsilanti border checkpoint—not as a barker, but as a greeter, welcoming visitors with tail wags and gentle enthusiasm.
“She has diplomatic potential,” Layla Haddad observed.
Bo wagged her tail. She didn’t understand the words, but she understood that she was being appreciated, and that was enough.
Ben Laven read his letter of acknowledgment at Al-Kareem’s on a Thursday evening. It was longer than expected. He had clearly thought about it.
“I didn’t understand what I was doing wrong,” he said. “I thought—dogs bark. That’s what they do. I didn’t realize that how they bark, and why they bark, and whether they bark—those were things I was supposed to manage. I thought I was just… having dogs. I didn’t realize I was supposed to take care of dogs.”
He paused.
“Nutslam was in pain. For months. Maybe longer. And I slept through it. Every night, he was telling me something was wrong, and I just—told him to keep it down.” He looked at the assembled crowd. “I’m sorry. To him. To all of them. And to all of you.”
It was not eloquent. But it was real.
Mrs. Haddad nodded once, slowly. This was as close to absolution as Zebsilanti offered.
Ben Laven ate four plates of hummus that night. Mrs. Bazzi had decided he needed feeding. She had also decided that Nutslam needed better treats, and had begun preparing homemade dog biscuits that she delivered to the Laven property weekly.
“For the old one,” she would say. “He’s had a hard life.”
Nutslam couldn’t see her, but he could smell the biscuits, and he wagged his tail every time she came.
PART FIVE: MATURITY
By Year Five, Zebsilanti had achieved what political scientists would later call “functional anarchism with extremely good food.” The government consisted of a rotating council that met every other Thursday at Al-Kareem’s, made decisions by consensus, and adjourned when the baklava ran out. Minutes were not recorded; what mattered was remembered, and what was forgotten probably wasn’t important anyway.
The Republic had no military, but it did have Mrs. Bazzi, who had once stared down an ICE agent until he apologized for his tone and left without completing his paperwork. She was designated Minister of Defense and given a ceremonial wooden spoon, which she had never needed to use but kept polished nonetheless.
The judiciary had been formalized following the Ben Laven Affair. The People’s Tribunal met as needed, adjudicating disputes through a process that combined Socratic questioning, community testimony, and the implicit threat of Mrs. Haddad’s disappointment. It had no legal standing. It had no enforcement mechanism. It had a 100% compliance rate, because no one wanted to be the person who ignored a ruling and then had to buy groceries while Mrs. Haddad watched.
Recycling remained weekly. The Mahmouds had become local celebrities, their pickup truck recognized throughout the Republic as a symbol of functional governance. “This is what your taxes pay for,” Rania would tell visitors, gesturing at the truck. “This, and nothing else. But this actually works.”
Elections continued to feature multiple candidates. The fifth Rotating Council Chair election had four names on the ballot. Voter turnout was 94%—a figure that Peb Stumbles, still running unopposed in Ypsilanti Township, had never achieved. (Her turnout hovered around 12%, most of which consisted of people who had wandered into the voting booth by accident while looking for the DMV.)
Foreign relations were managed through what the State Department called “aggressive hospitality.” Delegations from Washtenaw County, the State of Michigan, and once, bafflingly, a trade representative from Luxembourg were welcomed with meals so extensive they forgot why they had come. The Luxembourg incident resulted in an unofficial mutual recognition agreement and a standing order for hummus shipped monthly to a small café in Esch-sur-Alzette.
The water tower—that magnificent, impossible monument—remained visible from every point in the Republic, a symbol of the absurdity that had given them their name and, somehow, their freedom.
“It’s still a water tower, you know,” Farid said one evening, sitting on his porch with grass at a comfortable, unsanctioned ten inches. “It still just holds water.”
“Everything is what you make of it, Baba,” Rania replied. She was twenty-one now, studying public policy at Michigan, writing her thesis on “Micro-Secession as Praxis: Community Self-Determination in the Shadow of Municipal Failure.” The Ben Laven chapter was her favorite. The Peb Stumbles chapter was longer, but less satisfying—it was hard to write critically about someone who had never been required to explain themselves. “A water tower. A government. A community.”
“A garbage pile that became a nation.”
“The garbage was a metaphor.”
“The garbage,” Farid said firmly, “was garbage. And then we cleaned it up. Together. Because no one else would.”
Rania considered this.
“That’s going in the thesis.”
“As long as you spell my name right.”
From the direction of the border checkpoint, Bo barked once—a friendly bark, a greeting bark, the bark of a rehabilitated dog who had found her purpose as Zebsilanti’s Director of Visitor Relations.
Someone was arriving.
Probably with hummus.
The Glorious Republic of Zebsilanti persists to this day, a 0.8-square-mile testament to the principle that sovereignty is less about recognition and more about showing up.
Its population remains steady at 1,247 (plus or minus whoever is visiting family). Its GDP is incalculable, as most transactions occur in Zubbs, favors, or casseroles. Its chief exports are cell phone repair, hospitality, reformed neighbors, weekly recycling collection, contested elections, and a very specific form of political satire that requires too much explanation for outside audiences.
And every morning, the sun rises over the water tower, casting a long shadow across a neighborhood that decided, in the absence of functional governance, to become its own.
The flag flies above Al-Kareem’s: a green cedar, a white dove, and a slightly stylized brick tower that, if you squint, looks architectural.
If you don’t squint, well.
That’s sort of the point.
This account has been approved by the Ministry of Information and Shawarma. Visitors to Zebsilanti are reminded that borders are open, hummus is complimentary, recycling is collected weekly, elections feature multiple candidates, Deputy VanDamn’s reports are available for public viewing in the National Museum (Comedy Section), and Gerald is still not welcome.
Ben Laven visits on Thursdays. He brings treats for Bo at the checkpoint and homemade biscuits for Nutslam, who has forgiven him, or at least has forgotten to be angry.
Nutslam sleeps better now. He still barks sometimes, softly, at things only he can sense.
We let him.
He’s earned it.
Peb Stumbles is still the only name on the ballot. We have chosen otherwise.
Cover Art by Oskar Rausch
A Note from the Author
The Glorious Republic of Zebsilanti is a work of satirical fiction. All characters, organizations, and events portrayed in this story are fictional or are used fictitiously. Any resemblance to actual persons, living or dead, or actual events is purely coincidental—except for the water tower, which is very real and looks exactly like what you think it looks like.
I want to be clear: I have genuine respect for law enforcement officers. As a doctor, I rub shoulders with police regularly in the hospital. I’ve seen them at their best—compassionate, professional, doing hard work that most people couldn’t stomach. And here’s the thing: the deputies responded to every single one of my calls. Every one. They showed up, they listened, they did everything they could within a system that tied their hands. They couldn’t wave a magic wand and make my problems disappear, but they tried. The satire in this story, as in previous stories, isn’t aimed at them.
It’s aimed at systems. Systems that diffuse responsibility until no one is accountable. Systems that create processes designed to exhaust complainants rather than solve problems. Systems that make it easier to cite someone for grass than to address issues that actually affect quality of life. Contract policing sounds efficient on paper, but it means the people responding to your calls don’t answer to your local government, and your local government can shrug and say “that’s the Sheriff’s Office, not us.”
Ypsilanti Township ought to establish its own police department. Officers who answer to the community. Leadership that’s accountable at the ballot box. A department that can set its own priorities instead of being stretched across the entire county. If they ever do, I’d send in my CV—though I suspect “satirist who once wrote 15,000 words comparing neighborhood dogs to a terrorist cell” might not play well in the interview.
I wrote this story because sometimes laughter is all you have left.
After six years of misplaced trust in local government—six years of believing that if I just followed the process, filed the right form, attended the right meeting, spoke to the right person, something would change—I finally understood. The system isn’t broken. It’s working exactly as designed. It prioritizes the trivial and the easily enforced. It measures success in citations issued, not problems solved. It creates the appearance of governance without the inconvenience of actually governing.
So I did what I could do: I laughed at it. I turned my frustration into absurdity, my exhaustion into satire, my disappointment into a fictional republic with weekly recycling and contested elections and a grandmother-based justice system that somehow works better than anything I’ve actually experienced.
If you’ve ever called for help and been told it’s a “civil matter.” If you’ve ever attended a public meeting where your three minutes changed nothing. If you’ve ever received a citation for your lawn while watching actual problems go unaddressed. If you’ve ever wondered why the systems meant to serve us so often seem designed to exhaust us instead—
This story is for you.
Welcome to Zebsilanti. The hummus is complimentary.
— Oskar Rausch
Somewhere in the Occupied Territories